CCTV Cybersecurity Sydney: Securing Remote Access and Networks
In an age where technology permeates every aspect of our lives, the significance of cybersecurity cannot be overstated, especially concerning Closed-Circuit Television (CCTV) systems. These systems, once considered merely a tool for surveillance, have evolved into complex networks that can be vulnerable to cyber threats. As businesses and individuals increasingly rely on CCTV for security, the potential risks associated with inadequate cybersecurity measures become more pronounced. Cybercriminals are constantly developing new methods to exploit weaknesses in these systems, making it imperative for users to understand the importance of safeguarding their CCTV networks.
The ramifications of a compromised CCTV system can be severe. Unauthorized access can lead to the manipulation of camera feeds, allowing intruders to bypass security measures or engage in illicit activities without being detected. Moreover, sensitive footage can be stolen or tampered with, leading to privacy violations and potential legal repercussions. Therefore, understanding the importance of CCTV cybersecurity is not just about protecting physical assets; it is also about preserving the integrity and confidentiality of information that these systems capture. As such, organizations must prioritize cybersecurity as an integral part of their overall security strategy.
In the realm of CCTV cybersecurity, ensuring secure remote access and protecting networks is crucial for safeguarding sensitive information. A related article that delves into the importance of security measures in monitoring systems is titled “Pros and Cons of Active Back to Base Alarm Monitoring in Sydney.” This article provides valuable insights into the benefits and potential drawbacks of alarm monitoring, which can be essential for understanding how to enhance overall security protocols. For more information, you can read the article here: Pros and Cons of Active Back to Base Alarm Monitoring in Sydney.
Securing Remote Access for CCTV Systems
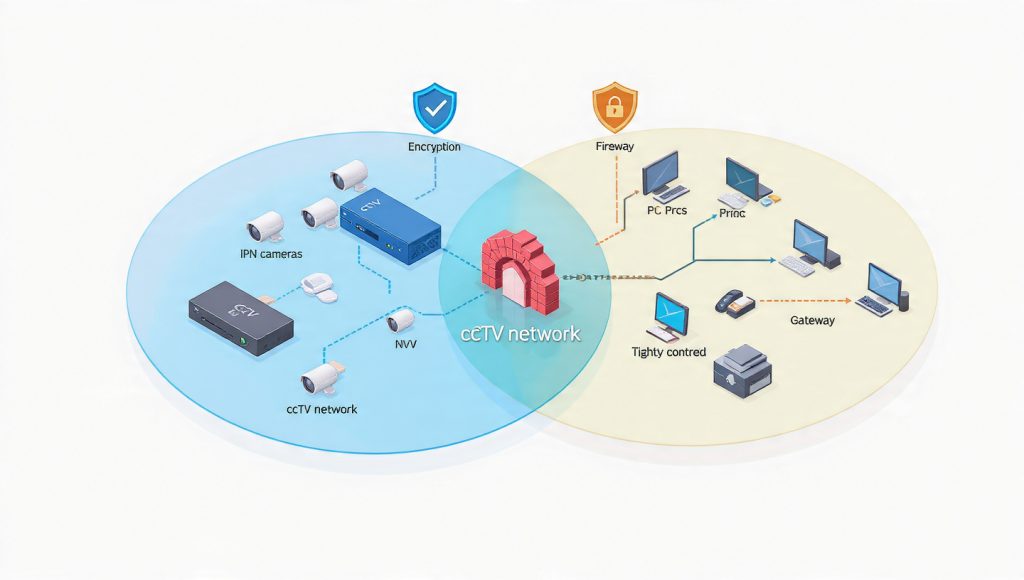
With the advent of remote monitoring capabilities, users can now access their CCTV systems from virtually anywhere in the world. While this convenience enhances security management, it also introduces new vulnerabilities. Securing remote access to CCTV systems is crucial to prevent unauthorized users from gaining entry. One effective method is to implement Virtual Private Networks (VPNs), which create a secure tunnel for data transmission, ensuring that only authorized personnel can access the system remotely.
Additionally, employing strong passwords and changing them regularly can significantly reduce the risk of unauthorized access. Passwords should be complex, incorporating a mix of letters, numbers, and special characters. Furthermore, organizations should consider limiting remote access to specific IP addresses or locations, thereby adding another layer of security. By taking these proactive measures, users can enjoy the benefits of remote monitoring while minimizing the risks associated with cyber threats.
Protecting Networks from Cyber Threats
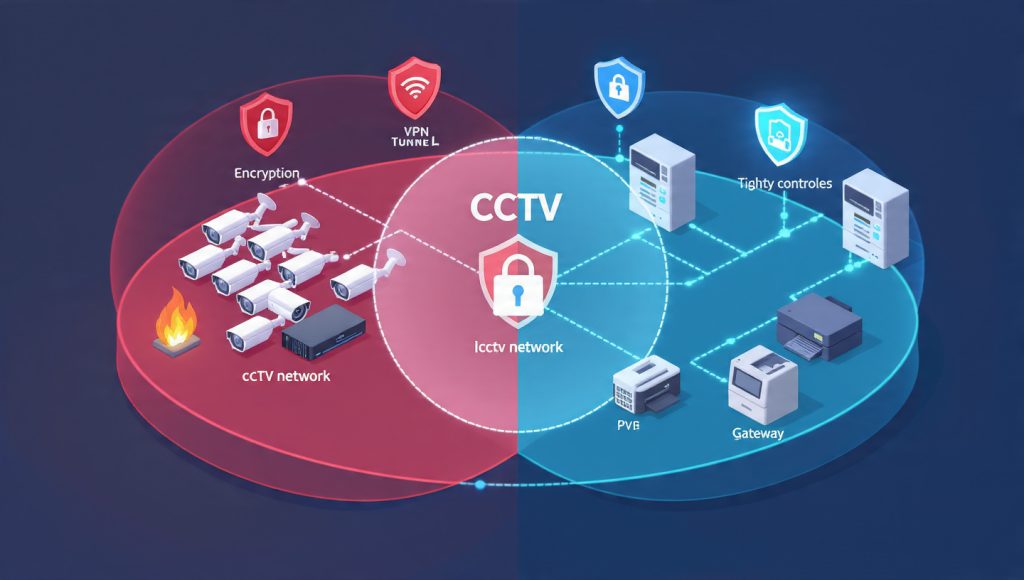
The security of CCTV systems is intrinsically linked to the overall health of the network they operate on. Protecting networks from cyber threats requires a multi-faceted approach that includes firewalls, intrusion detection systems, and regular network assessments. Firewalls act as a barrier between trusted internal networks and untrusted external networks, filtering out potentially harmful traffic. Intrusion detection systems monitor network activity for suspicious behavior and alert administrators to potential breaches.
Moreover, organizations should conduct regular vulnerability assessments to identify and address weaknesses in their network infrastructure. This proactive approach not only helps in mitigating risks but also ensures that any emerging threats are promptly dealt with. By fortifying the network on which CCTV systems operate, organizations can create a robust defense against cyber threats that could compromise their surveillance capabilities.
Implementing Multi-factor Authentication for CCTV Systems

Multi-factor authentication (MFA) has emerged as a critical component in enhancing the security of CCTV systems. By requiring users to provide multiple forms of verification before accessing the system, MFA adds an additional layer of protection against unauthorized access. This could involve a combination of something the user knows (like a password), something they have (such as a smartphone or security token), or something they are (biometric verification).
Implementing MFA significantly reduces the likelihood of unauthorized access, even if a password is compromised. For instance, if an intruder manages to obtain a user’s password through phishing or other means, they would still need the second form of authentication to gain access to the CCTV system. As cyber threats continue to evolve, adopting MFA is a proactive step that organizations can take to bolster their security posture and protect sensitive surveillance data.
In the realm of CCTV cybersecurity in Sydney, securing remote access and networks is crucial for protecting sensitive data and maintaining system integrity. A related article discusses the importance of intercom systems in enhancing security measures, which can complement CCTV installations effectively. For more insights on how these systems can work together to bolster your security framework, you can read more about it in this informative piece on intercom systems.
Ensuring Encryption of CCTV Data

Data encryption is a fundamental aspect of cybersecurity that should not be overlooked when it comes to CCTV systems. Encryption transforms data into a format that is unreadable without the appropriate decryption key, ensuring that even if data is intercepted during transmission or storage, it remains secure from prying eyes. This is particularly important for CCTV footage, which may contain sensitive information about individuals and activities.
Organizations should ensure that both data at rest (stored footage) and data in transit (footage being transmitted over networks) are encrypted. Utilizing strong encryption protocols such as AES (Advanced Encryption Standard) can provide robust protection against unauthorized access. By prioritizing encryption, organizations can safeguard their CCTV data from potential breaches and maintain the confidentiality of their surveillance operations.
In the realm of CCTV cybersecurity, particularly in Sydney, ensuring secure remote access and robust network protection is paramount for safeguarding sensitive data. A related article that delves into the importance of access control systems can be found at this link, which highlights how implementing effective access control measures can significantly enhance overall security protocols. By integrating these systems with CCTV solutions, businesses can create a comprehensive security strategy that addresses both physical and digital vulnerabilities.
Regularly Updating CCTV Software and Firmware

Peace of mind is our priority.Keeping CCTV software and firmware up to date is essential for maintaining system security and functionality. Manufacturers frequently release updates that address vulnerabilities and improve performance. Failing to apply these updates can leave systems exposed to known exploits that cybercriminals may leverage to gain unauthorized access.
Organizations should establish a routine schedule for checking and applying updates to their CCTV systems. This includes not only the cameras themselves but also any associated software used for monitoring and management. By staying current with software and firmware updates, organizations can significantly reduce their risk of falling victim to cyber threats while ensuring that their surveillance systems operate at peak efficiency.
Monitoring and Managing CCTV System Access

Effective management of access to CCTV systems is crucial for maintaining security integrity. Organizations should implement strict access controls that define who can view or manage surveillance footage and under what circumstances. This includes creating user roles with varying levels of permissions based on job responsibilities, ensuring that only authorized personnel have access to sensitive information.
Regular audits of user access logs can help identify any unusual activity or unauthorized attempts to access the system. Additionally, organizations should have protocols in place for promptly revoking access when employees leave or change roles within the company. By actively monitoring and managing access to CCTV systems, organizations can mitigate risks associated with insider threats and ensure that surveillance data remains secure.
Training Employees on Cybersecurity Best Practices for CCTV Systems

The human element is often the weakest link in cybersecurity defenses, making employee training an essential component of any security strategy involving CCTV systems. Organizations should invest in comprehensive training programs that educate employees about cybersecurity best practices specific to surveillance technology. This includes recognizing phishing attempts, understanding the importance of strong passwords, and knowing how to report suspicious activity.
Regular training sessions can help reinforce these concepts and keep employees informed about emerging threats and trends in cybersecurity. By fostering a culture of cybersecurity awareness within the organization, employees become active participants in protecting CCTV systems rather than passive observers. Ultimately, well-informed employees are better equipped to recognize potential threats and respond appropriately, enhancing the overall security posture of the organization.
In conclusion, as technology continues to advance, so too do the methods employed by cybercriminals seeking to exploit vulnerabilities in CCTV systems. Understanding the importance of cybersecurity in this context is paramount for organizations looking to protect their assets and sensitive information. By implementing robust security measures such as securing remote access, protecting networks from threats, utilizing multi-factor authentication, ensuring data encryption, regularly updating software, managing system access effectively, and training employees on best practices, organizations can create a comprehensive defense against potential cyber threats. In doing so, they not only safeguard their surveillance capabilities but also foster a culture of security awareness that permeates throughout their operations.